Overview
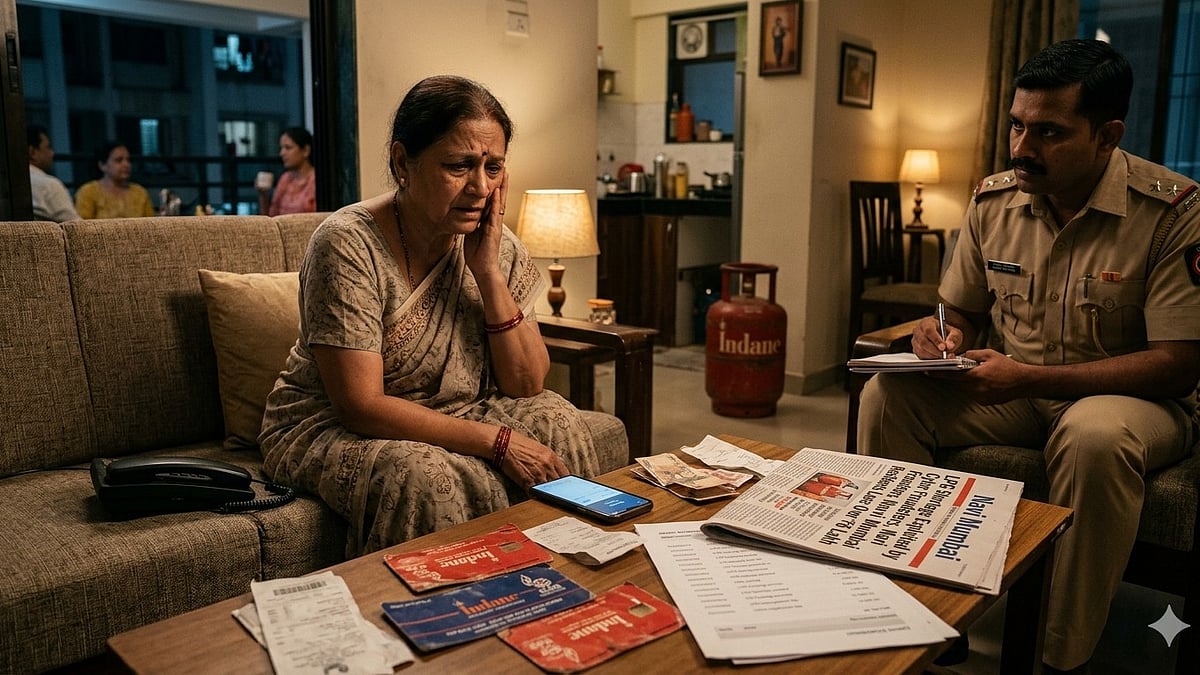
Cyber fraudsters operating in Navi Mumbai, India, have been reported exploiting public concern over LPG (liquefied petroleum gas) shortages as a social-engineering pretext to target residents. Impersonating officials from Mahanagar Gas Limited (MGL), the attackers distributed malware-laced links through WhatsApp, ultimately compromising victims' smartphones and gaining unauthorized access to their bank accounts. At least three residents have been confirmed as victims, with aggregate financial losses exceeding ₹6 lakh (approximately USD 7,200).
Attack Vector and Methodology
The campaign follows a classic social-engineering pattern tailored to a regional utility anxiety:
- Impersonation: Attackers posed as representatives of Mahanagar Gas Limited, a well-known piped and LPG gas utility, lending credibility to their outreach.
- Pretext: Victims were approached under the guise of resolving or registering concerns related to ongoing LPG shortages — a timely and emotionally resonant lure.
- Malware Delivery: Malicious links were sent via WhatsApp, a widely used messaging platform in India. Victims who clicked and downloaded the linked content inadvertently installed malware on their devices.
- Device and Account Compromise: Once installed, the malware enabled attackers to access victims' phones and associated banking applications or credentials, facilitating unauthorized financial transfers.
Incidents and Law Enforcement Response
Formal cases have been registered at police stations in Nerul and Kamothe, both located within the Navi Mumbai jurisdiction. Local law enforcement authorities have acknowledged the incidents and are actively investigating. Police have issued public advisories urging residents to exercise extreme caution and avoid downloading files or clicking links received from unknown or unverified sources, particularly those claiming to be from utility providers.
Threat Intelligence Assessment
This campaign is consistent with a broader pattern of utility-themed phishing and smishing operations observed across South Asia, where threat actors exploit infrastructure anxieties — such as power outages, gas shortages, or billing disputes — to manipulate targets into executing malicious payloads. The use of WhatsApp as a delivery mechanism reflects the platform's dominant penetration in Indian mobile usage, making it an attractive vector for mobile-targeted malware campaigns.
- Target Profile: General public, particularly individuals with active LPG or piped gas connections.
- Platform Abused: WhatsApp (link-based malware distribution).
- Impact: Device compromise, credential theft, unauthorized banking transactions.
- Geography: Navi Mumbai, Maharashtra, India.
Recommendations
- Do not click on links received via WhatsApp or SMS from unknown or unverified contacts, even if they claim to represent a utility company.
- Verify any official communication by calling the utility provider's published customer care number directly.
- Enable two-factor authentication (2FA) on banking and financial applications.
- Install reputable mobile security software capable of detecting and blocking malicious downloads.
- Report suspicious messages to local cybercrime authorities or the national cybercrime portal (cybercrime.gov.in).
Source
Free Press Journal — LPG Shortage Exploited By Cyber Fraudsters, Navi Mumbai Residents Lose Over ₹6 Lakh